Understanding the Offensive
Development Practitioner Certification
(ODPC) - Live Training
White Knight Labs proudly presents the Offensive Development Practitioner Certification (ODPC), an intermediate-level, live training course designed for cybersecurity professionals looking to enhance their offensive development skills. This program is not for beginners; it’s tailored for those aiming to elevate their expertise in offensive cybersecurity through hands-on labs and real-time guidance from experienced instructors.
This live training format provides two intensive days of interactive instruction, allowing participants to engage directly with instructors and peers while learning advanced techniques in offensive development. Our curriculum is dynamically updated to incorporate the latest research and methodologies, ensuring you stay ahead of the curve.
November 14th & November 15th 2024
Course Syllabus
- Terraform Lab Deployment in students’ AWS environments
- Guacamole Walkthrough
- Portable Executable Primer
- Windows API Primer
- Converting PE Files to Shellcode (Donut, Windows-Only Tools)
- Process Injection: CreateRemoteThread
- Shellcode Storage (text section)
- Shellcode Storage (resources section)
- Process Injection: Process Hollowing
- Process Injection: Early Bird
- Process Injection: MockingJay
- Windows API Direct Syscalls
- Windows API Indirect Syscalls
- Hiding Imports via Dynamic Resolution
- XOR Encrypting API Function Calls
- Introduction to Cobalt Strike
- Cobalt Strike C2 Deep Dive (Profiles and BOFs)
- Defeating Sandbox Detection
- Identifying an EDR’s Active Protection
- DLL Proxying for Persistence
- API Unhooking
- AMSI Primer & AMSI Bypass
- ETW Primer & Process Injection: Caro-Kann
- Custom Reflective DLL Loaders
- App Domain Injection
- ClickOnce Payload Development
Prerequisites
To ensure participants are prepared for the ODPC Live Training, students must meet the following prerequisites:
- Programming Background: Proficiency in C, C++, or C# is crucial for understanding complex code structures discussed in the course.
- Understanding of C2 Frameworks: Familiarity with how Command and Control (C2) frameworks operate.
- Basic Process Injection Techniques: Knowledge of basic process injection techniques.
- Shellcode Usage: Experience using shellcode in offensive operations.
- Payload Development Experience: Prior experience in developing payloads or creating footholds on target endpoints.
- Desire to Learn: Motivation to engage with advanced content and complete challenging labs.
- Aspiration to Bypass Security Measures: An interest in techniques to bypass AV and EDR systems.
What You’ll Learn
By enrolling in the Offensive Development Practitioner Certification (ODPC) – Live Training, you’ll gain:
- Understanding Modern Defenses: Learn to overcome modern security mechanisms through live, interactive labs with instructor guidance. You’ll get hands-on experience in Terraform labs, PE file conversions, and advanced process injection strategies.
- Advanced Offensive Techniques and Cobalt Strike: Develop expert-level skills in offensive development, including deep dives into Cobalt Strike C2 frameworks, sandbox detection evasion, and EDR bypass strategies.
- Custom Payload Development: Learn to build and deploy custom reflective DLL loaders, bypass AMSI and ETW protections, and create tailored offensive payloads, with instructors guiding you through each step.
Who Should Enroll
This course is ideal for:
- Penetration Testers, Red Teamers, and Blue Teamers: Looking to advance their malware development skills.
- Cybersecurity Professionals: Aiming to effectively deploy offensive security tools in complex scenarios.
- Security Analysts and Researchers: Interested in deepening their understanding of offensive development methodologies.

Course Takeaways
By the end of this course, you will have:
- A comprehensive understanding of modern cybersecurity defenses and how to bypass them.
- Advanced skills in offensive techniques, including Cobalt Strike C2 usage and custom payload development.
- Practical, hands-on experience with dynamically updated labs in AWS environments, with expert guidance throughout the process.
Dynamic Attack Paths and Labs
In the Offensive Development Practitioner Certification (ODPC) – Live Training, you will engage in real-time, hands-on lab environments that simulate real-world offensive operations. Throughout the two-day course, instructors will walk you through each step of the attack paths and help you refine your techniques.
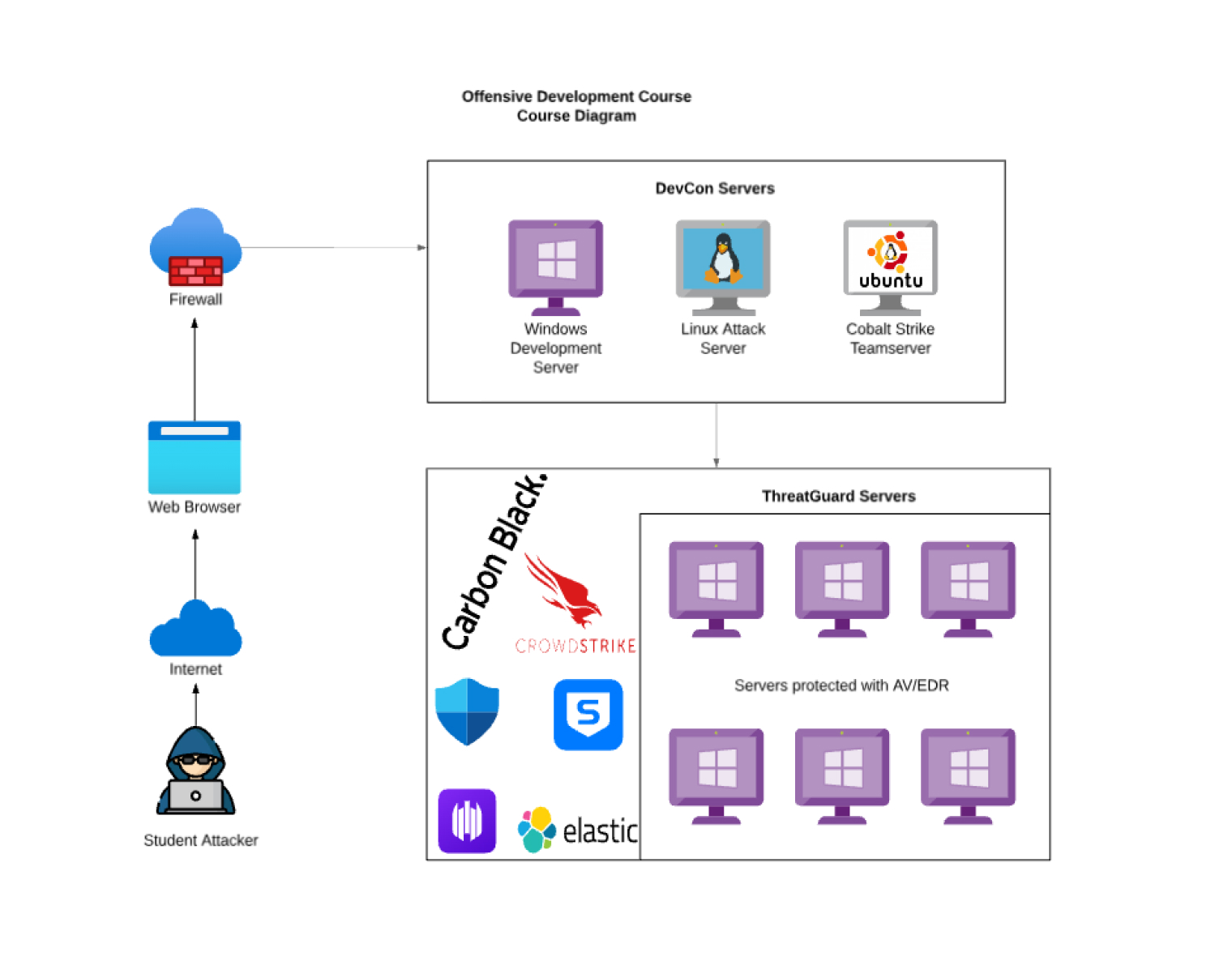
Lab Setup Overview
The lab setup includes a dynamic environment that mirrors real-world red team operations. The diagram represents the structure of the attack simulation, including:
- Cobalt Strike C2 Server: The main command and control server for your red team activities, which you will configure with instructor guidance.
- Windows Development Server: This server serves as your environment for developing and testing offensive payloads, with instructors providing insights on best practices.
- Linux Attack Server: Used to launch attacks and manage offensive operations.
- Multiple EDR-Protected Hosts: Attempt to bypass next-generation EDR systems and deliver your payloads while maintaining persistence.
Instructors will guide you through configuring this setup using Terraform in your AWS environment, providing insights into how these components interact in a real-world scenario.
The Offensive Development Practitioner Certification (ODPC) – Live Training is priced at $700. This fee includes access to live, instructor-led training, hands-on labs, and one exam voucher.
Cost and Discounts
The Offensive Development Practitioner Certification (ODPC) – On-Demand is priced at $500. This fee includes access to expert-created instructional materials, unlimited access to self-managed labs, and one exam voucher.
Additional Costs
- Compute Costs: Students are responsible for the AWS compute costs associated with running their lab environment.
Discounts Available
We offer a 20% discount to the following groups:
- Veterans and Active Military Personnel: Honoring those who have served or are currently serving.
- Students: Supporting the next generation of cybersecurity professionals.
- Educators: Recognizing the vital role of teachers in fostering cybersecurity knowledge.
- First Responders: Acknowledging the efforts of those who serve on the front lines in emergencies.
To take advantage of the discount, please email training-team@whiteknightlabs.com with proof of eligibility, and we’ll provide you with a custom discount code.
Register Now to take advantage of our special pricing and begin your journey toward mastering Azure security!
Frequently Asked Questions (FAQs)
The live training course is conducted over two intensive days, with each day running from 8:30 AM to 5:00 PM EST.
Participants should have a solid understanding of programming (C, C++, or C#), C2 frameworks, process injection, shellcode, and experience with payload development.
Yes, participants must have an AWS account for lab deployment.
Yes, all participants will receive comprehensive course materials, including instructional videos, step-by-step lab walkthroughs, code snippets, and Terraform scripts for cloud infrastructure deployment.
Instructors will be available throughout the live training to provide real-time feedback, answer questions, and troubleshoot any issues you encounter during the labs.
Yes, you will have lifetime access to your labs. This means you can continue practicing and refining your skills without any time constraints.
The certification exam is a hands-on, practical test where you will be required to demonstrate your skills in bypassing EDR systems and deploying offensive techniques.
Yes, an exam voucher is included with your course registration, allowing you to schedule your certification exam at your convenience.
No, the exam voucher does not expire, allowing you to take the exam at your convenience whenever you feel ready.
Register Now for the Next Live Training Session
Next session: November 14th & November 15th 2024
Class Times: 8:30 AM EST – 5:00 PM EST
Secure your seat now and receive additional details by email once you complete the registration.